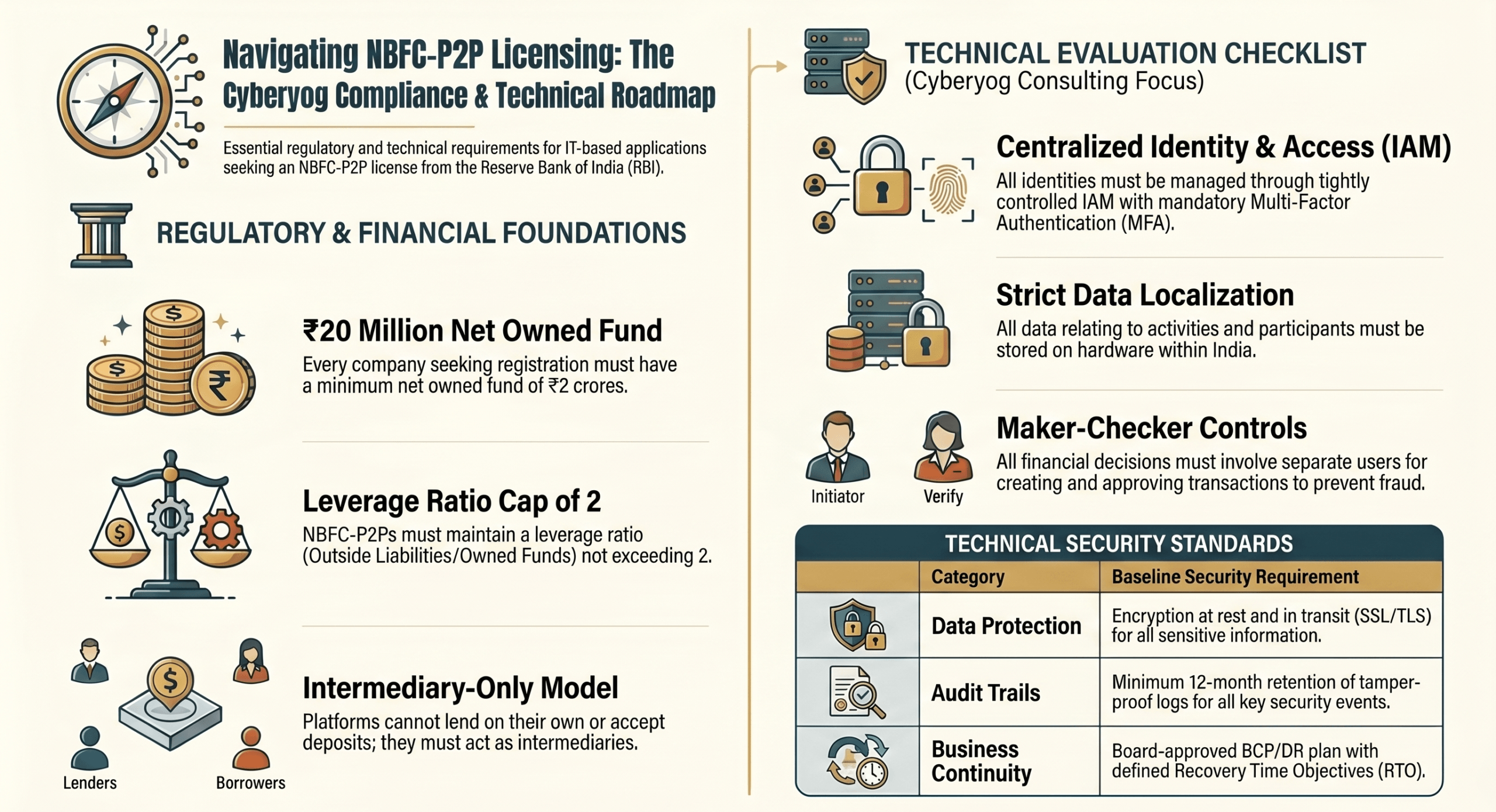
To guide your IT development and license application, we have structured this consultation based on the mandatory technical evaluation categories required for P2P platforms:
1. Authentication and Authorization
- Authentication: Your platform must centrally manage all identities through a tightly controlled Identity and Access Management (IAM) system, handling provisioning, validation, and single sign-on where possible. You must implement Multi-Factor Authentication (MFA) requiring users to provide something they know (User ID) and something they have (OTP). Furthermore, service-to-service authentication should utilise Digital Certificates or session tokens for the exchange of sensitive data.
- Authorization: Access to protected resources must be governed by Role-Based Access Control (RBAC), ensuring that users inherit access rights based on their specific group memberships. It is critical to implement the Principle of Least Privilege, meaning user accounts and developers only hold the minimum privileges necessary for their tasks. For all financial systems, “Maker-Checker” controls (Segregation of Duties) must be embedded within the core application so that the creator and approver of any transactional decision are separate individuals.
2. Audit Trails and Centralized Logging
- Audit Trails: Your application must log all key events across the Network, Operating System, Database, and Application layers. This includes authentication successes and failures (with source IP addresses), password changes, and any transactions impacting Sensitive Personal Information (SPI).
- Centralized Logging: The platform must support log aggregation by integrating with a Centralised Syslog or Security Information and Event Management (SIEM) system in real time. Database level administrative changes and security modifications (like Web Application Firewall rules) must also be securely logged and restricted to authorized personnel to prevent tampering by super users.
3. Data Protection, Data Security, and Data Localisation
- Data Protection: Access to data should be controlled by security attributes using RBAC at the database level. You must enforce end-to-end encryption for all sensitive data during transit using secured communication mediums (like SSL/IPSEC), and all sensitive information must be securely encrypted at rest.
- Data Security & Localisation: You must restrict the usage of collected customer data strictly to providing core services, without sharing it with third parties or providing unsolicited services. As per regulatory mandates, all sensitive data (including personal and financial information of borrowers and lenders) must remain within India’s geographical boundaries, and all data traffic must be restricted to the India region. You must also ensure that data ownership strictly remains with your entity in any vendor agreements.
4. Operating Environment and Web Services Security
- Operating Environment: Your network architecture must include LAN zoning (network segmentation) to isolate different zones using firewalls and VLANs. We highly recommend designing your infrastructure in line with a “Zero Trust Architecture”, which assumes implicit trust is revoked and strictly verifies every user and device before granting access to internal resources. You must also implement Segregation of Duties between software development teams, IT operations, and security compliance teams.
- Web Services Security: Security policies for APIs and web services should be enforced externally through an intermediary, such as an API Gateway, utilising token-based authorisation (e.g., AWS Cognito).
- Vulnerability & Patch Management: You must establish an automated Anti-malware system and conduct continuous Vulnerability Assessments and Penetration Testing (VAPT) to identify weaknesses at the component level.
5. Business Continuity Planning (BCP) / Disaster Recovery (DR) and High Availability
- BCP/DR: The architecture design must natively support High Availability to ensure critical business applications remain operational. You must implement a Disaster Recovery Plan aligned with business-approved Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) to restore services quickly during a disruption.
6. P2P Specific Requirements
- Fair Practices and Transparency: Your application algorithms must be free of unfair practices and biases that favour certain customers over others. Sharing and using data must rely on explicit customer consent.
- Public Disclosures: The website must publicly disclose your credit assessment/score methodology, data protection policies, grievance redressal mechanisms, portfolio performance (including Non-Performing Assets), and broad business model.
- Data Masking: When disclosing borrower details to lenders (e.g., required amount, credit score, interest rate), or lender details to borrowers, you must strictly protect and exclude their personal identities and contact details.
- CIC Integration: Your IT system must be integrated with all Credit Information Companies (CICs) for regular data submission.
- Mandatory Disclaimer: The platform must display a caveat stating that the Reserve Bank of India does not accept responsibility for the correctness of statements on the platform and provides no assurance for the repayment of loans. The RBI’s name and logo should not be used misleadingly elsewhere on the site.
7. Regulatory Compliance and Audit Report
- Compliance Requirements: The platform must comply with the RBI’s “Master Directions – Non-Banking Financial Company – Peer to Peer Lending Platform” regulations. You are required to maintain archiving and audit logging policies that store audit logs for a minimum of 12 months in a tamper-proof environment.
- Audit Report: Following the in-principle approval from the RBI, you must be prepared to submit external Information Systems (IS) audit reports.
8. Cloud Adoption Policy and Third-Party Risk Assessment
- If your infrastructure is cloud-based, you must establish a cloud adoption policy governing the vendor lifecycle. Implement a centralised Third-Party Risk Management (TPRM) process to periodically conduct risk analysis on your service providers. Your Master Services Agreements (MSAs) must incorporate clauses granting you the “right to audit” and mandating vendor compliance with your Information Security policies and RBI regulations.
By ensuring your IT app and website infrastructure address each of these baseline evaluation categories, your platform will be technically sound and fully prepared for the RBI licensing process.