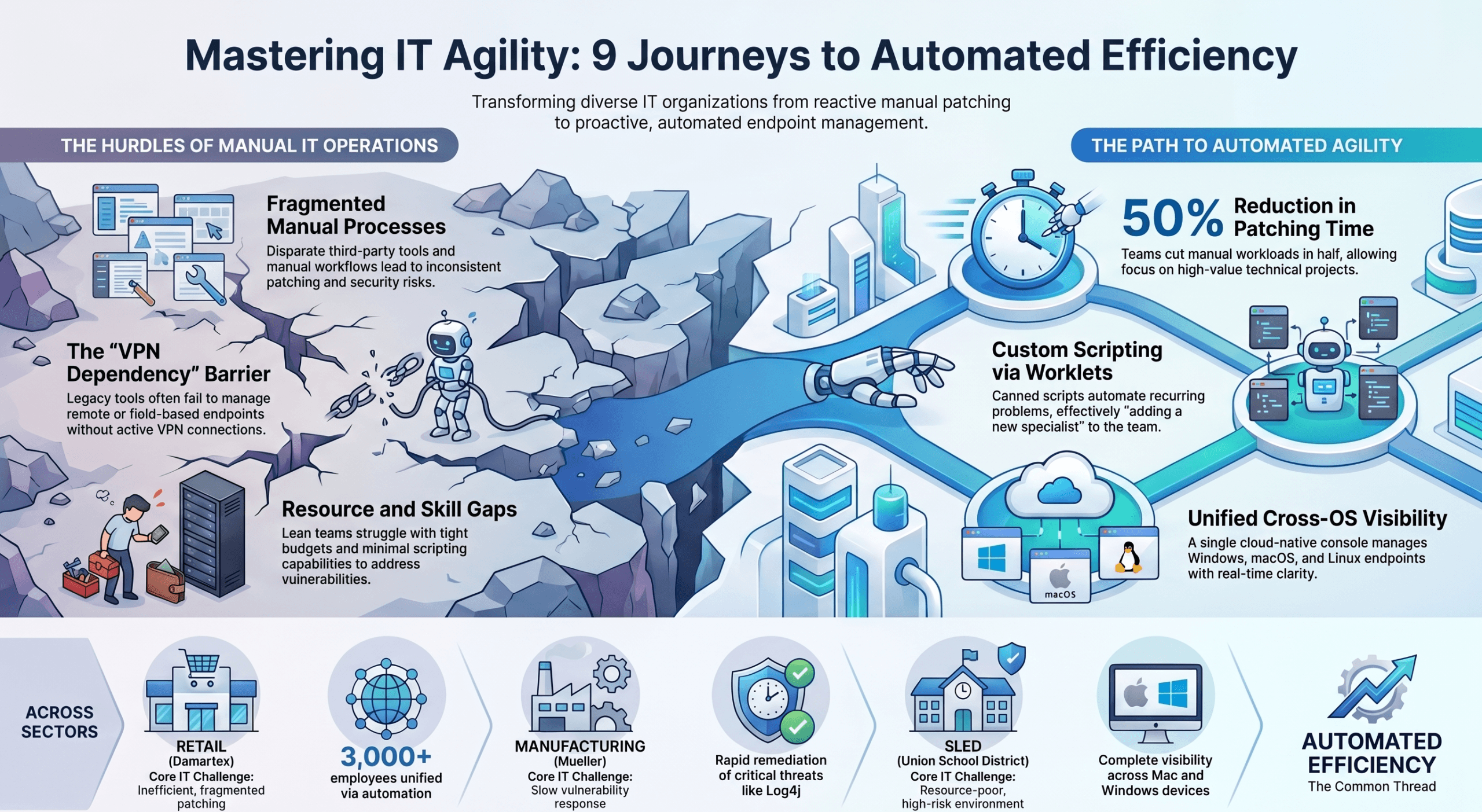
Automox is an IT automation platform that empowers modern organizations to slash cost and complexity while winning back valuable hours for their IT professionals.
Continue readingSlide Deck: DPDP vs GDPR – Global Privacy Frameworks
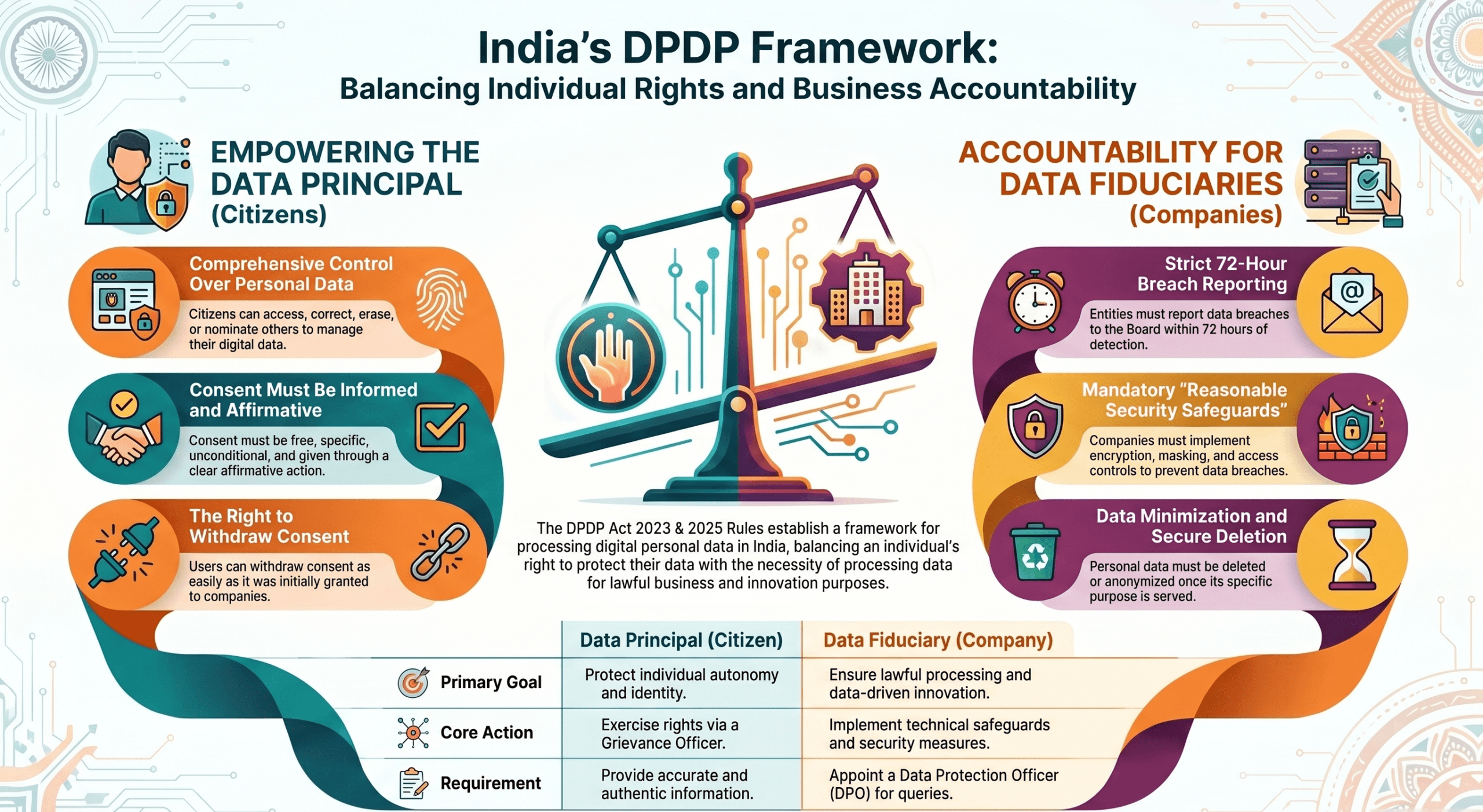
Exclusively on India’s Digital Personal Data Protection (DPDP) Act, 2023, and its 2025 Rules. Information regarding the EU’s General Data Protection Regulation (GDPR) and the cultural comparisons between India and Europe is drawn.
Continue readingSlide Deck: Workspace DLP Blueprint
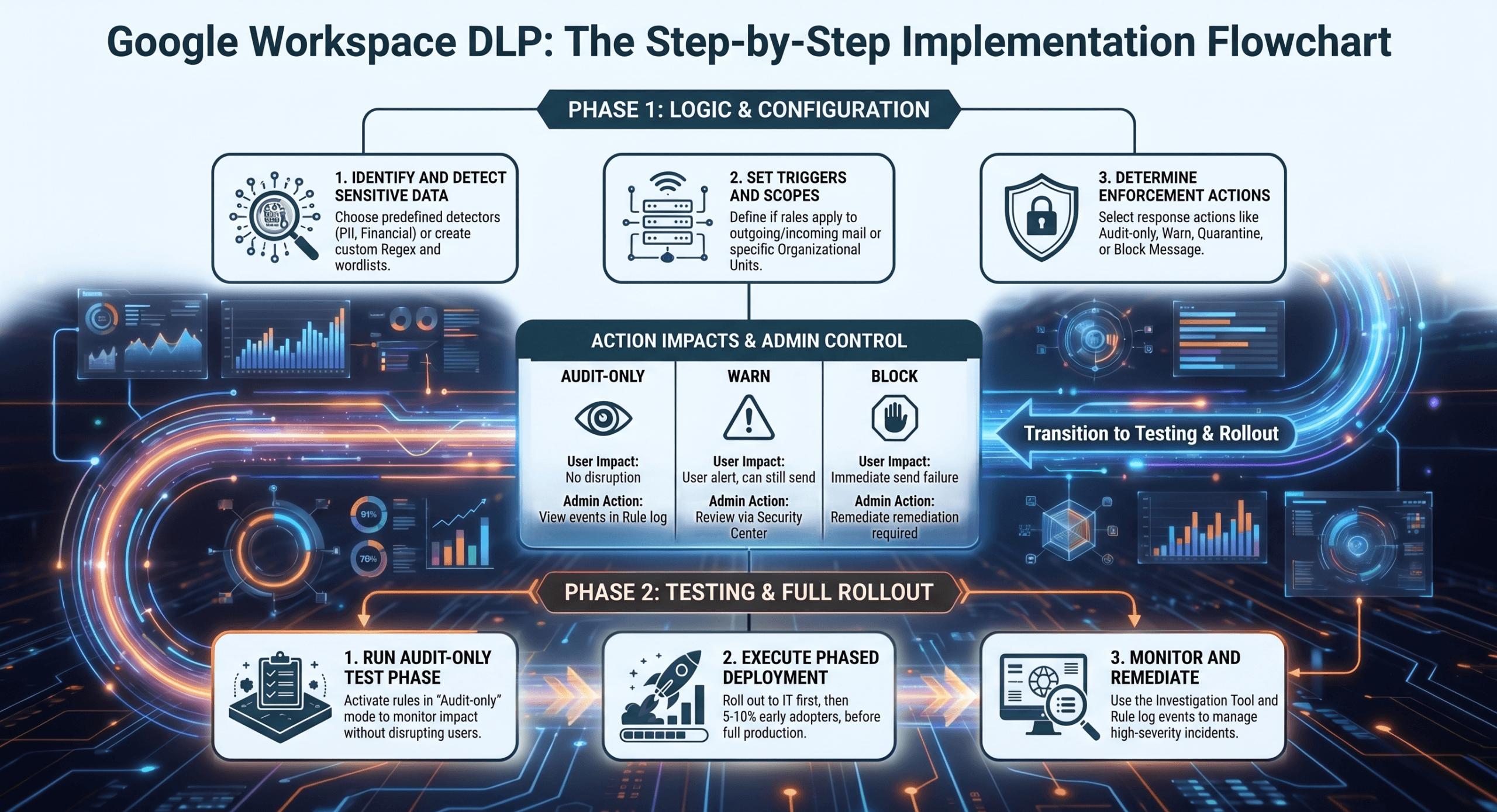
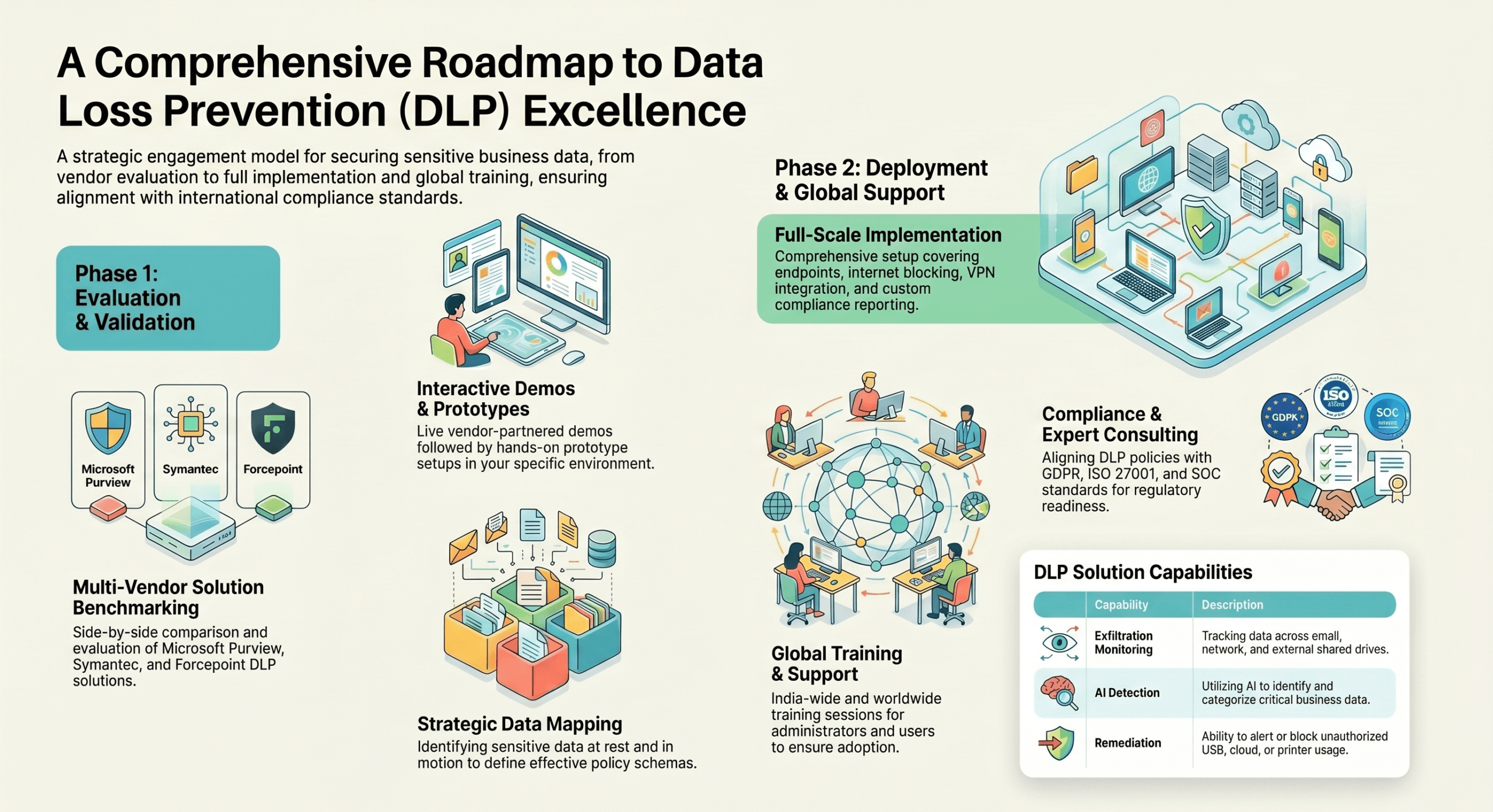
Here is a comprehensive DLP Compliance Audit and Implementation Checklist detailing what an Administrator must configure and manage to protect PII, PHI, and PCI (credit card) data across Google Workspace applications (like Google Drive, Gmail, and Google Sheets).
Continue readingSlide Deck: HIPAA_Compliance_Architecture (Part 2)
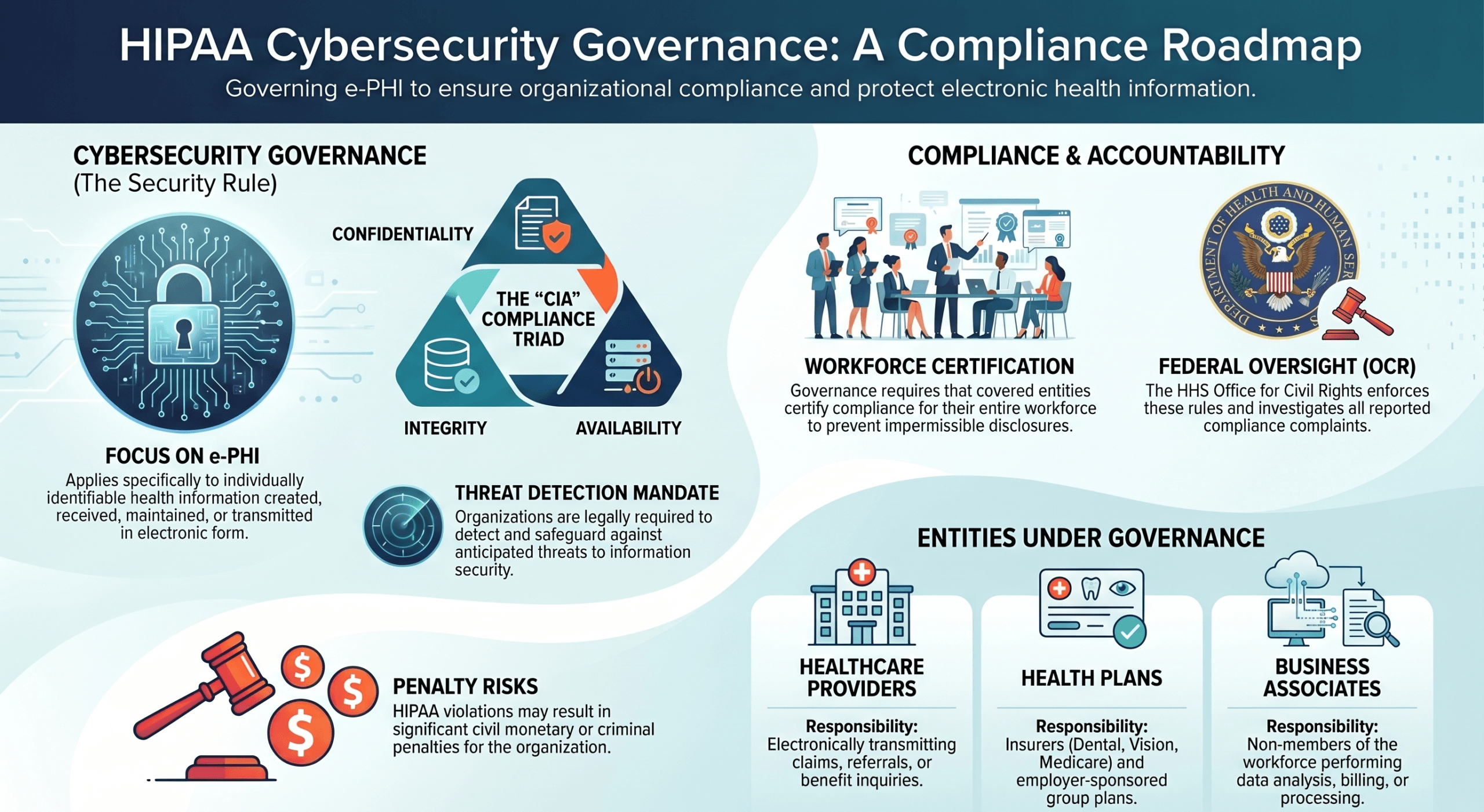
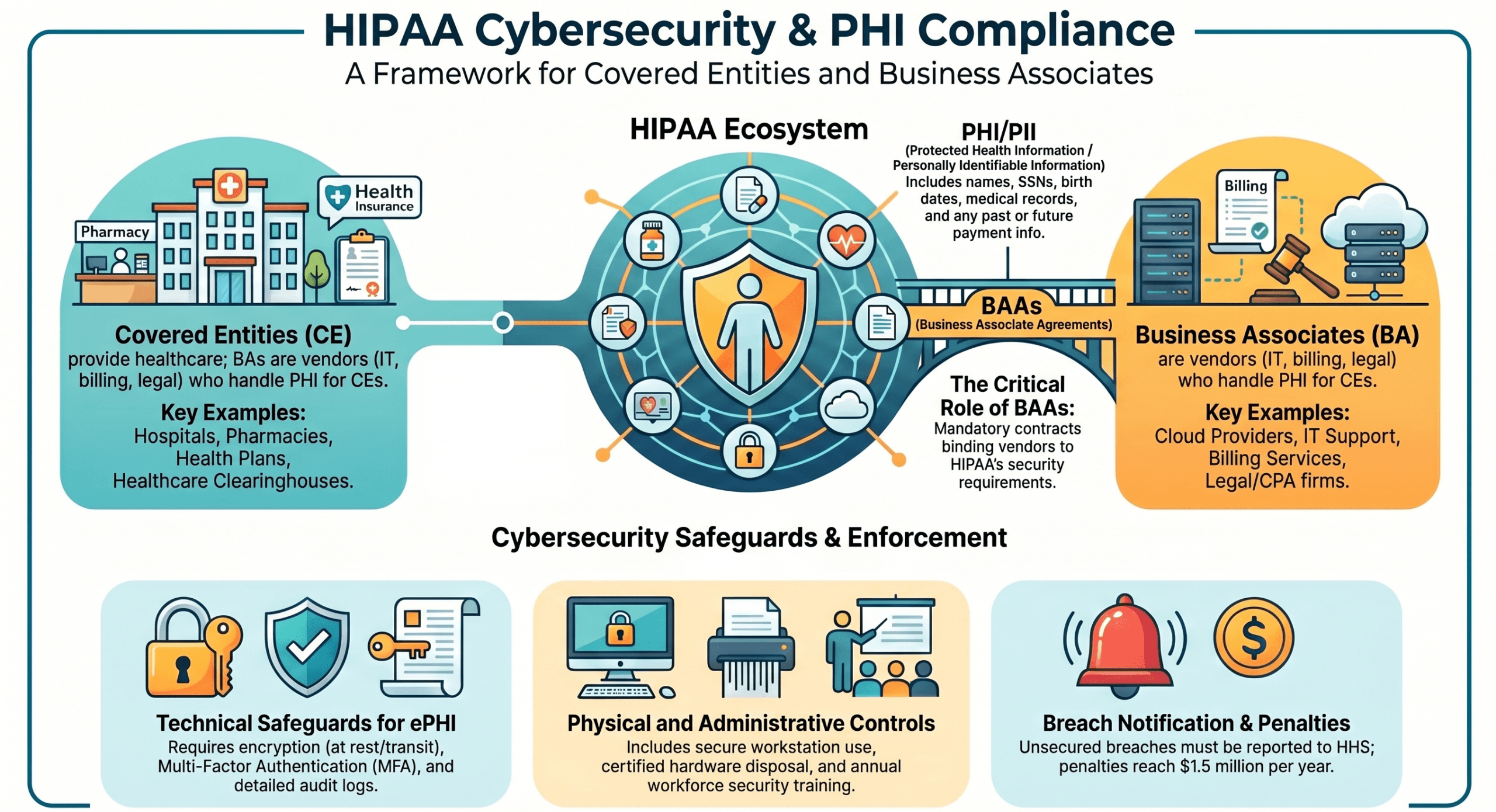
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) establishes foundational federal standards designed to protect sensitive health information from being disclosed without a patient’s consent. When focusing specifically on cybersecurity, compliance, and governance, your primary concern is the HIPAA Security Rule.
Continue readingSlide Deck: HIPAA_Compliance_Architecture (Part 1)
In the U.S. healthcare system, the Health Insurance Portability and Accountability Act (HIPAA) sets the federal standard for protecting sensitive patient data. When focusing on cybersecurity, compliance centers around protecting this data from unauthorized access, breaches, and cyberattacks while ensuring it remains available for patient care.
Continue readingSlide Deck: Enterprise_DLP_Blueprint
Cyberyog Technologies provides specialized consulting, audits, and readiness assessments for several key compliance frameworks that form the regulatory foundation of a Data Loss Prevention (DLP) strategy.
Continue readingSlide Deck: The_Resilience_Blueprint
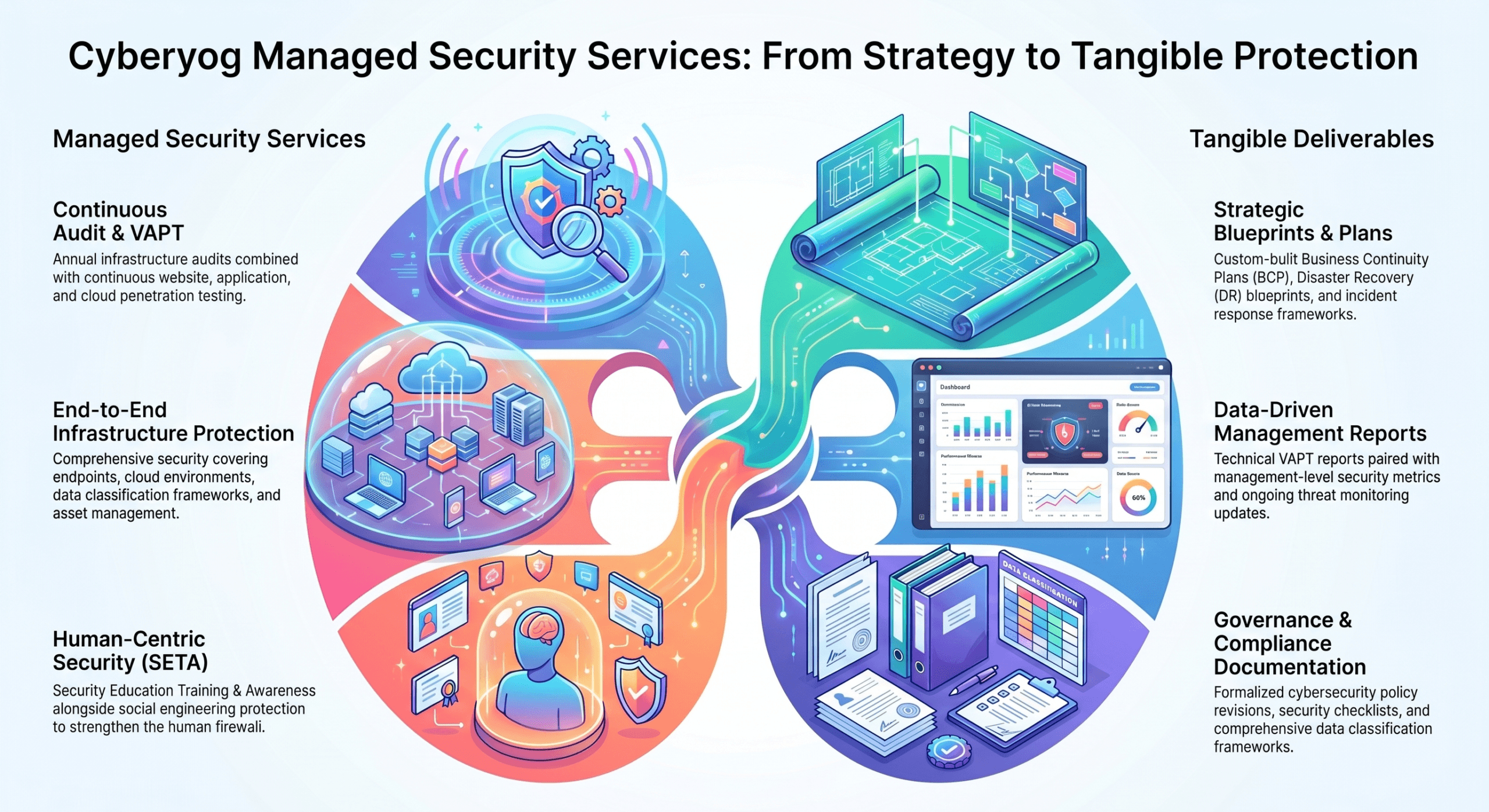
Your need for Annual InfoSec Audits and Cybersecurity Metrics aligns perfectly with Cyberyog’s core offerings, which include dedicated InfoSec Audits and Information Systems Audits that comply with accepted industry standards and frameworks.
Continue readingSlide Deck: RBI_P2P_Licensing_Blueprint
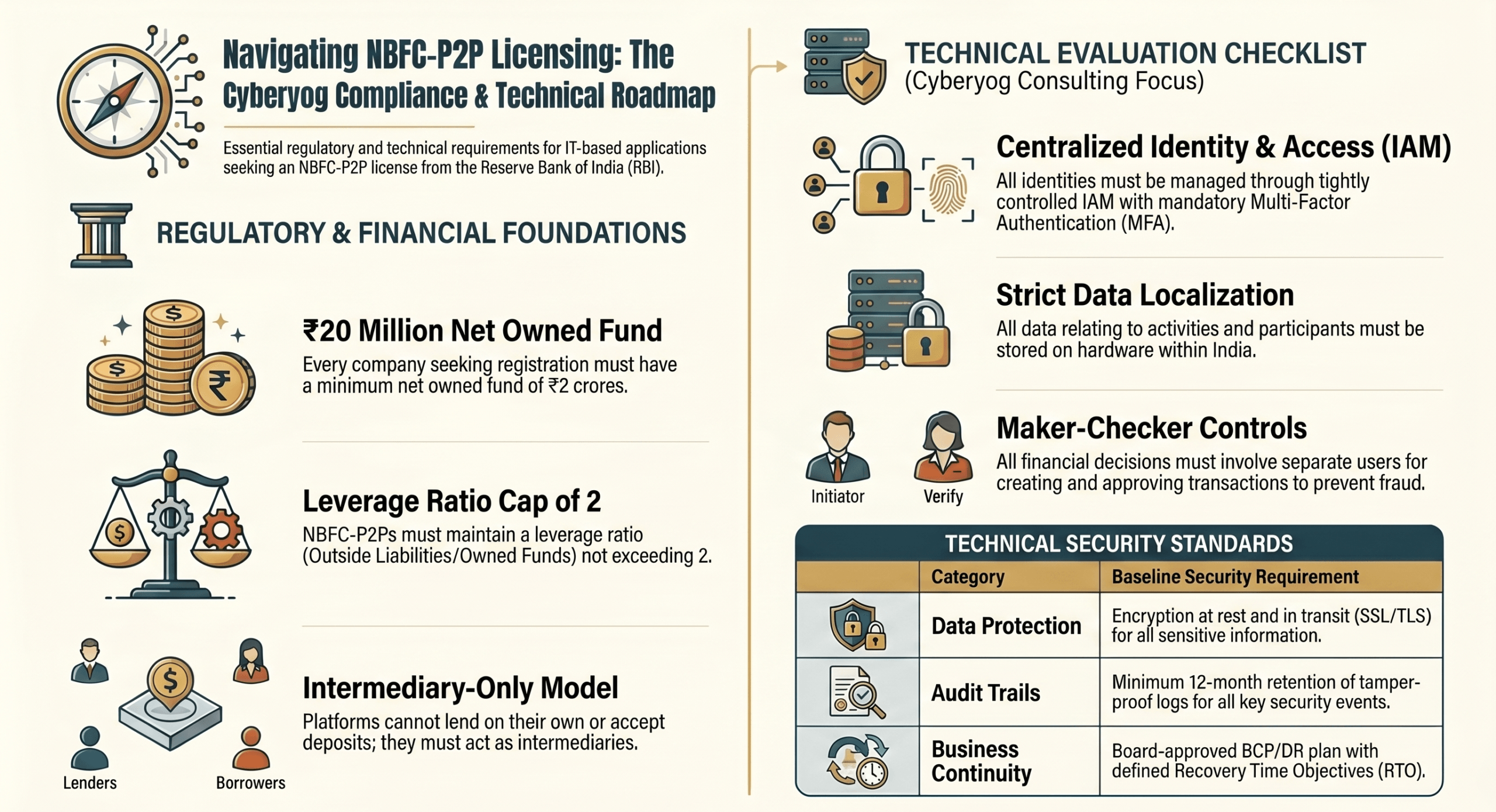
To successfully apply for a Peer-to-Peer (P2P) lending license from the Reserve Bank of India (RBI), your IT-based application or website must be underpinned by a robust, secure, and compliant technological framework.
Continue readingSlide Deck: Digital_Security_Blueprint
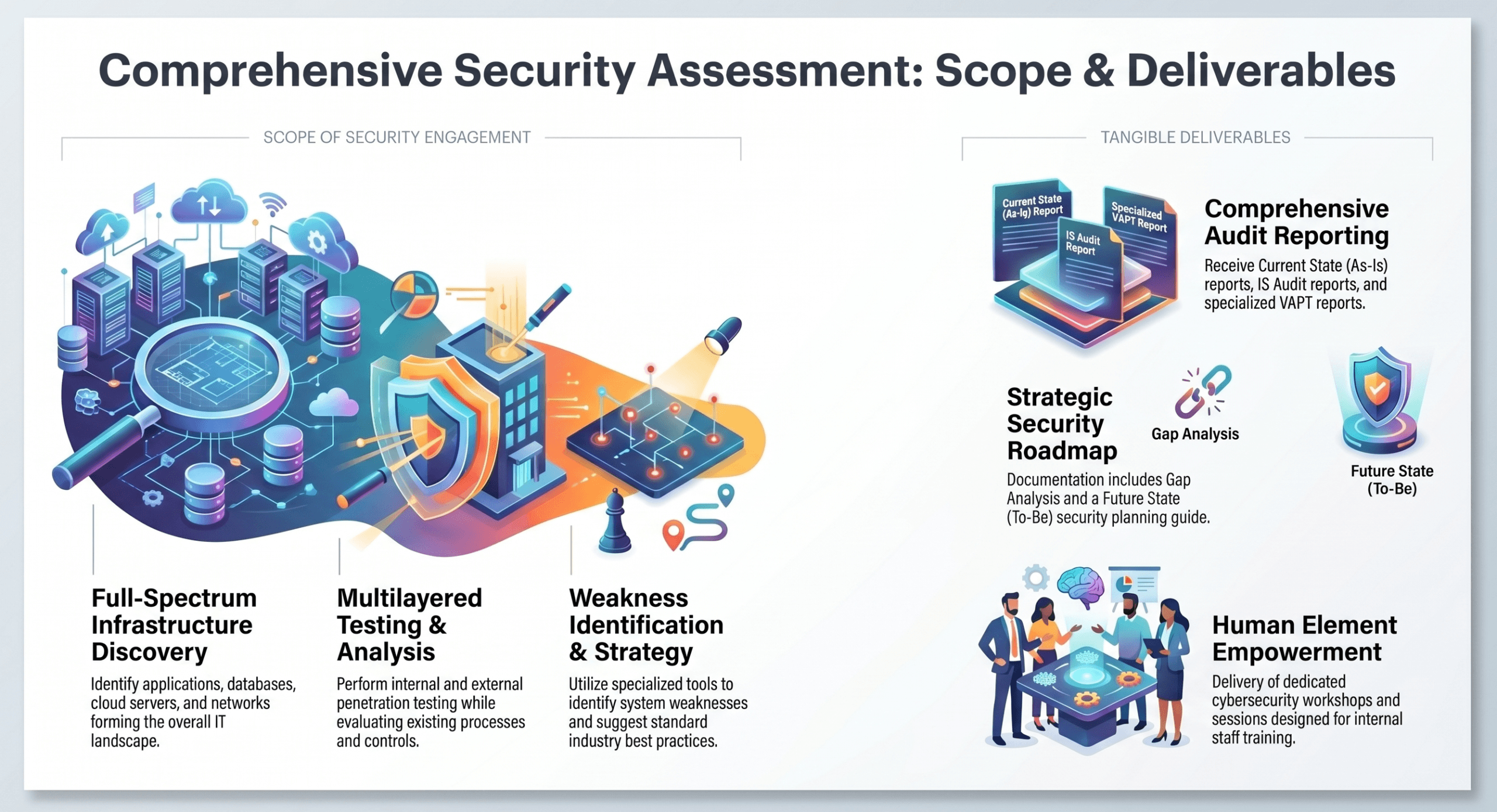
Cyberyog provide tangible written materials—including Website/Internal VAPT Reports, a Current State (As-Is) Report, a Future State (To-Be) projection, and a Gap Analysis with a Security Roadmap – leveraging their “Know Your CyberScore” methodology.
Continue readingSlide Deck: Cyber Resilience Blueprint
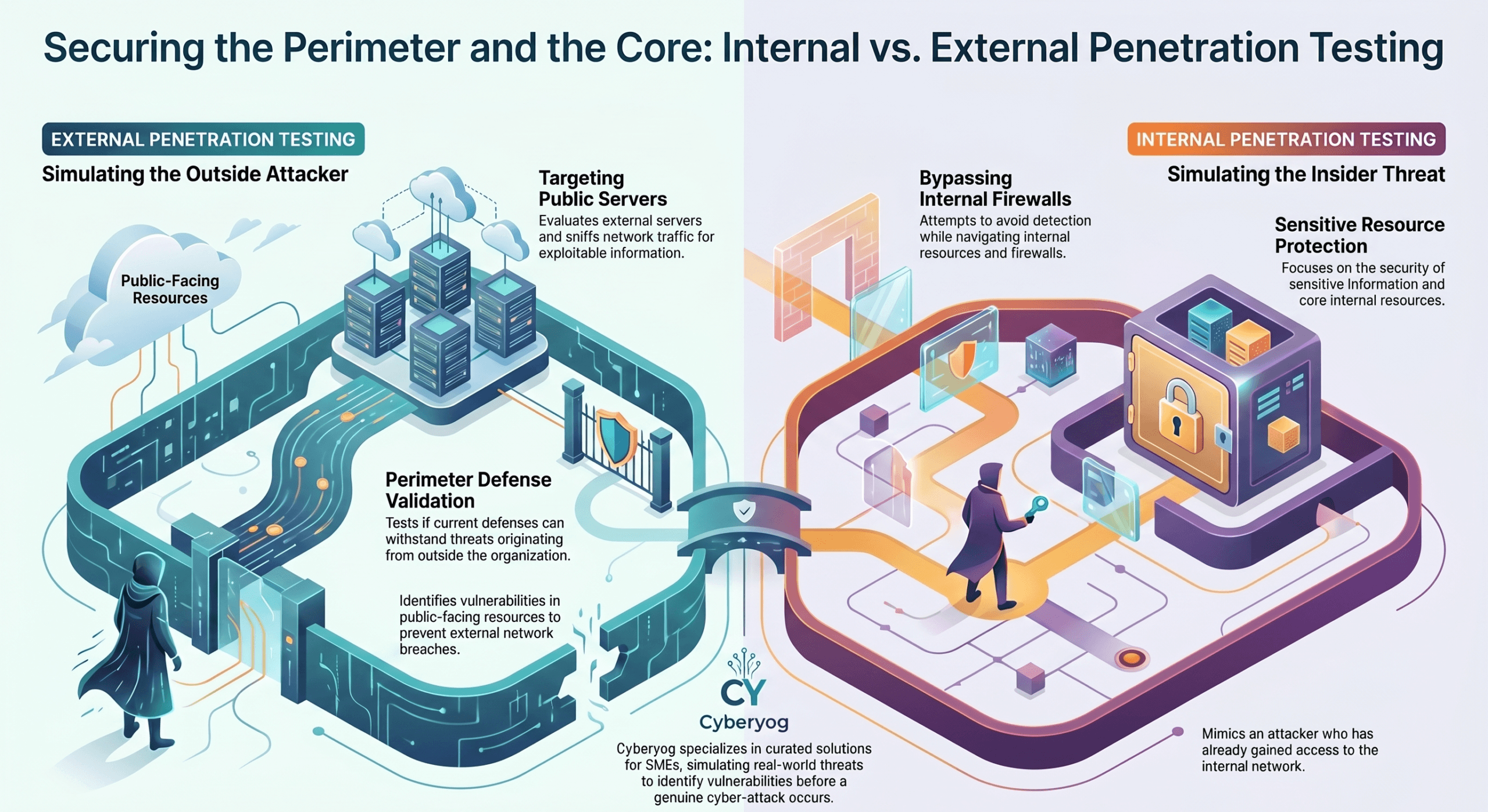
Cyberyog provides external penetration testing by simulating outside threats attempting to breach a client’s network through methods like searching for public-facing servers, sniffing traffic, and exploiting external resources.
Conversely, their internal penetration testing simulates an inside threat aiming to access sensitive information while actively trying to evade detection from internal network defenses such as firewalls.