If you live in India and use online shopping or food delivery apps, chances are you have seen a message like this: “Your parcel is on hold. Please confirm your address using the link below.” The message looks routine, harmless, and urgent. That is exactly why this scam keeps working.
The first reason is timing. Indians receive a huge number of legitimate delivery updates every week from e commerce platforms, courier companies, and hyperlocal services. Scammers take advantage of this habit. When a message arrives saying there is an issue with a package, most people assume it is related to something they recently ordered and click without thinking twice.
The second trick is imitation. Scam messages often copy the tone, language, and branding style of real courier services. Some even use sender names that resemble logistics companies. Once the victim clicks the link, they are taken to a fake website that asks for personal details, mobile numbers, or small “re delivery fees.” That is enough to capture card details or trigger UPI fraud.
A common real life example seen across Indian cities is the fake India Post or courier reschedule link. Users report being asked to pay as little as twenty or thirty rupees. The amount feels insignificant, so people proceed. Behind the scenes, the page is harvesting card data or setting up future fraud attempts.
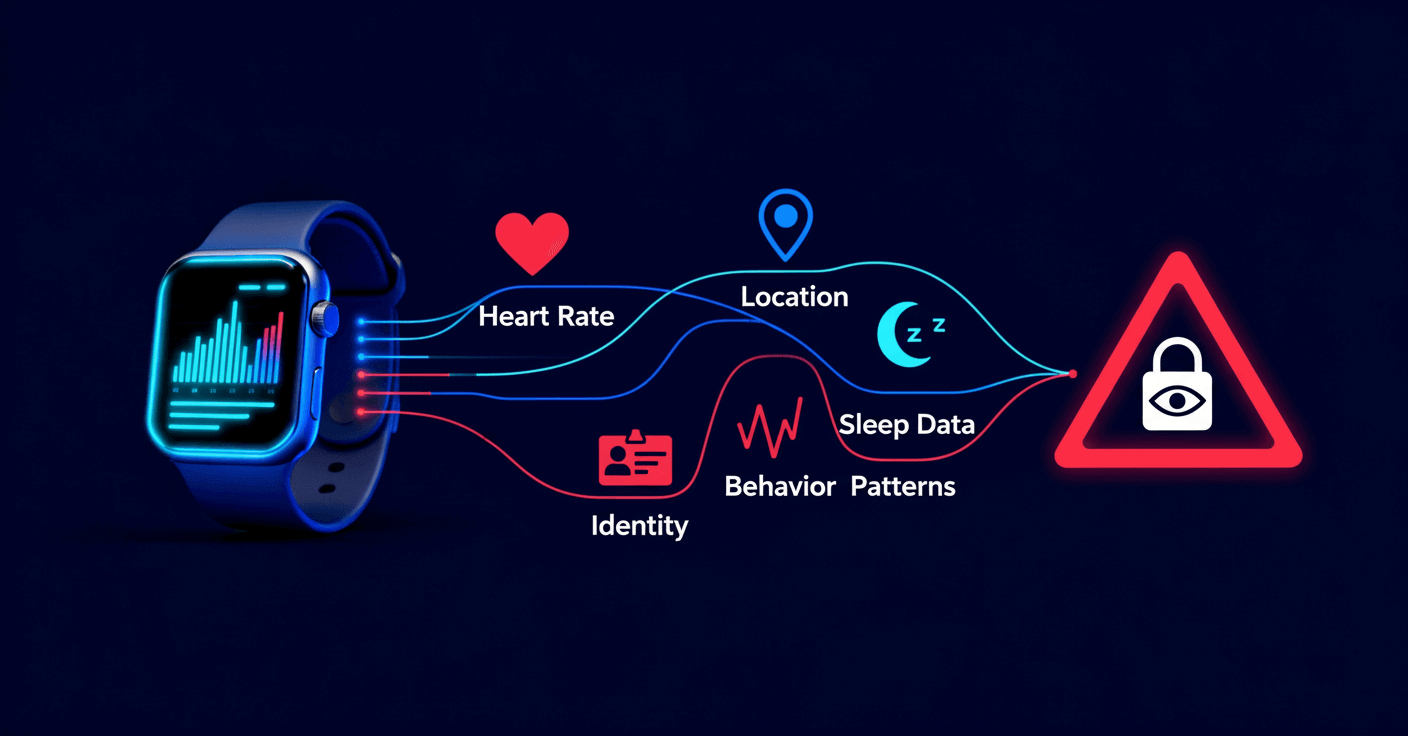
Another reason this scam works is data availability. Scammers already have access to leaked phone numbers and shopping behavior from previous breaches. That allows them to target people who are more likely to be expecting deliveries, making the messages feel personal and believable.
Finally, urgency does the psychological heavy lifting. Messages warn that parcels will be returned or orders cancelled within hours. Urgency shuts down rational thinking and pushes quick action.
This scam is not about technology alone. It is about manipulating everyday habits. For businesses, it highlights the need for stronger customer communication controls and better protection of user data. For individuals, it is a reminder that real delivery companies do not ask for payments or sensitive details through random links. In cybersecurity, the weakest link is rarely the system. It is human attention, stretched thin by convenience and speed.